CCNA – Switch Questions 2
Here you will find answers to Switch Questions – Part 2
Question 1
In which circumstance are multiple copies of the same unicast frame likely to be transmitted in a switched LAN?
A. after broken links are re-established
B. in an improperly implemented redundant topology
C. when upper-layer protocols require high reliability
D. during high traffic periods
E. when a dual ring topology is in use
Answer: B
Explanation
If we connect two switches via 2 or more links and do not enable STP on these switches then a loop (which creates multiple copies of the same unicast frame) will occur. It is an example of an improperly implemented redundant topology.
Question 2
An administrator would like to configure a switch over a virtual terminal connection from locations outside of the local LAN. Which of the following are required in order for the switch to be configured from a remote location? (Choose two)
A. The switch must be configured with an IP address, subnet mask, and default gateway.
B. The switch must be connected to a router over a VLAN trunk.
C. The switch must be reachable through a port connected to its management VLAN.
D. The switch console port must be connected to the Ethernet LAN.
E. The switch management VLAN must be created and have a membership of at least one switch port.
F. The switch must be fully configured as an SNMP agent.
Answer: A C
Explanation
In order to remote access to a switch from outside of the local LAN (in a different subnet) we have to:
+ Configure an IP address on a VLAN on that switch, this VLAN is known as the management VLAN (it is usually VLAN 1)
+ Specify the default gateway for that switch so that it can send traffic to this gateway
Below shows an example of configuring remote access for a switch (suppose the management VLAN on the switch is 192.168.1.10/24 and the default-gateway IP address is 192.168.1.254)
Switch(config)#ip default-gateway 192.168.1.254
Switch(config)#interface vlan 1
Switch(config)#ip address 192.168.1.10 255.255.255.0
Switch(config)#no shutdown
Question 3
Refer to the exhibit. A junior network administrator was given the task of configuring port security on SwitchA to allow only PC_A to access the switched network through port fa0/1. If any other device is detected, the port is to drop frames from this device. The administrator configured the interface and tested it with successful pings from PC_A to RouterA, and then observes the output from these two show commands.
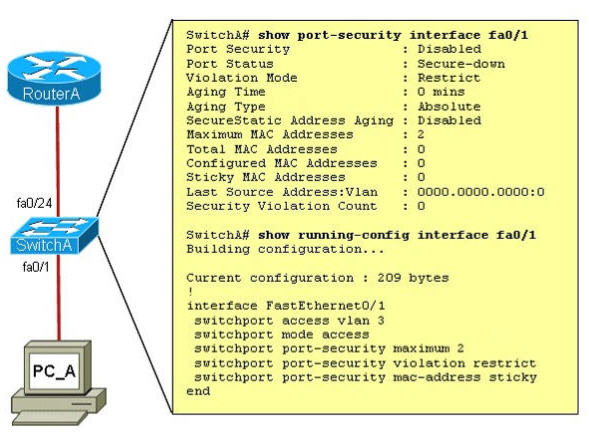
Which two of these changes are necessary for SwitchA to meet the requirements? (Choose two)
A. Port security needs to be globally enabled.
B. Port security needs to be enabled on the interface.
C. Port security needs to be configured to shut down the interface in the event of a violation.
D. Port security needs to be configured to allow only one learned MAC address.
E. Port security interface counters need to be cleared before using the show command.
F. The port security configuration needs to be saved to NVRAM before it can become active.
Answer: B D
Explanation
As we see in the output, the “Port Security” is in “Disabled” state (line 2 in the output). To enable Port security feature, we must enable it on that interface first with the command:
SwitchA(config-if)#switchport port-security
-> B is correct.
Also from the output, we learn that the switch is allowing 2 devices to connect to it (switchport port-security maximum 2) but the question requires allowing only PC_A to access the network so we need to reduce the maximum number to 1 -> D is correct.
Question 4
A company implements video conferencing over IP on their Ethernet LAN. The users notice that the network slows down, and the video either stutters or foils completely. What is the most likely reason for this?
A. minimum cell rate (MCR)
B. quality of service (QoS)
C. modulation
D. packet switching exchange (PSE)
E. reliable transport protocol (RTP)
Answer: B
Explanation
If the QoS is not configured correctly on the network, video traffic can slow down all your traffic. That company implemented video traffic and the network slows down -> maybe they don’t configure QoS so video traffic (which is very high and bursty) and data traffic have the same priority and video traffic eats all the bandwidth. QoS can solve this problem by giving higher priority for data (or voice) traffic over video traffic.
Question 5
Computer 1 is consoles into switch A. Telnet connections and pings run from the command prompt on switch A fail. Which of the following could cause this problem?
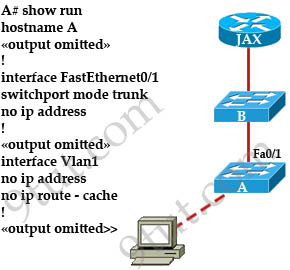
A. switch A does not have a cdp entry for switch B or router JAX
B. switch A does not have an IP address
C. port 1 on switch A should be an access port rather than a trunk port
D. switch A is not directly connected to router JAX
E. switch A does not have a default gateway assigned
Answer: B
Explanation
It’s a hard question to answer although it looks simple! From the output above we are sure that switch A does not have an IP address (on both Fa0/1 and on VLAN 1) so it can not ping or telnet to any other device -> B is correct.
Another answer seems to be correct is answer E – switch A does not have a default gateway assigned. We know that Switch A can not telnet to other device outside its subnet without having a default gateway. But the question only says “Telnet connections and pings run from the command prompt on switch A fail” without telling us where Switch A is trying to telnet or ping to. If it tries to connect to the outside network then E is correct. If it only want to connect to a device inside its subnet then a default gateway is not necessary.
So the best answer for this question is B!
Question 6
Refer to the exhibit. Give this output for SwitchC, what should the network administrator’s next action be?
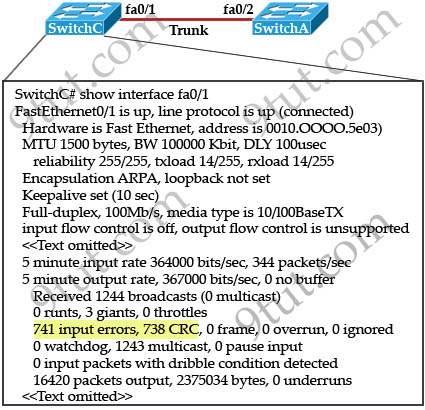
A. Check the trunk encapsulation mode for SwitchC’s fa0/1 port.
B. Check the duplex mode for SwitchC’s fa0/1 port.
C. Check the duplex mode for SwitchA’s fa0/2 port.
D. Check the trunk encapsulation mode for SwitchA’s fa0/2 port.
Answer: C
Question 7
Refer to the graphic
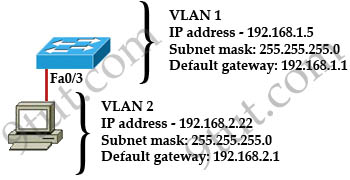
A host is connected to switch port Fa0/3 with a crossover cable. However, the port indicator on switch port Fa0/3 is not on, and the host can not communicate with hosts that belong to VLAN2 on the same switch. Based on the information given, where is the problem?
A. The switch has been assigned an incorrect subnet mask T1
B. Switch port Fa0/3 is not configured as a trunk port
C. Switch port Fa0/3 has been blocked by STP
D. The switch and the hosts must be in the same subnet
E. The cable type is wrong
Answer: E
Explanation
To specify when we use crossover cable or straight-through cable, we should remember:
Group 1: Router, Host, Server
Group 2: Hub, Switch
One device in group 1 + One device in group 2: use straight-through cable
Two devices in the same group: use crossover cable
In this case we connect a switch and a host so we need a straight-through cable -> E is correct.
Question 8
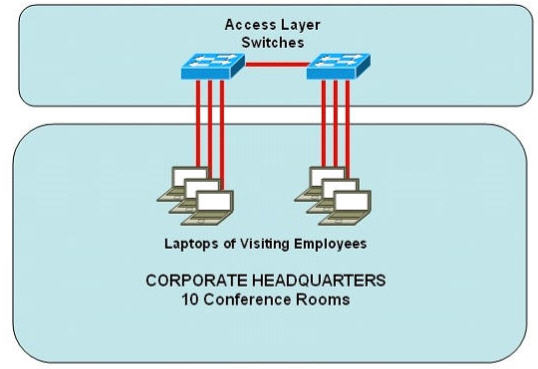
Refer to the exhibit. Some 2950 series switches are connected to the conference area of the corporate headquarters network. The switches provide two to three jacks per conference room to host laptop connections for employees who visit the headquarters office. When large groups of employees come from other locations, the network administrator often finds that hubs have been connected to wall jacks in the conference area although the ports on the access layer switches were not intended to support multiple workstations.
What action could the network administrator take to prevent access by multiple laptops through a single switch port and still leave the switch functional for its intended use?
A. Configure static entries in the switch MAC address table to include the range of addresses used by visiting employees.
B. Configure an ACL to allow only a single MAC address to connect to the switch at one time.
C. Use the mac-address-table 1 global configuration command to limit each port to one source MAC address.
D. Implement Port Security on all interfaces and use the port-security maximum 1 command to limit port access to a single MAC address
E. Implement Port Security on all interfaces and use the port-security mac-address sticky command to limit access to a single MAC address
F. Implement Port Security at global configuration mode and use the port-security maximum 1 command to allow each switch only one attached hub
Answer: D
Explanation
The Port Security filters frames based on its MAC so it can effectively prevent people connecting to the switch via hubs.
Question 9
Which of the following statements are true regarding bridges and switches? (Choose 3)
A. Switches are primarily software based while bridges are hardware based.
B. Both bridges and switches forward Layer 2 broadcasts.
C. Bridges are frequently faster than switches.
D. Switches have a higher number of ports than most bridges.
E. Bridges define broadcast domains while switches define collision domains.
F. Both bridges and switches make forwarding decisions based on Layer 2 addresses.
Answer: B D F
Question 10
A network administrator must configure 200 switch ports to accept traffic from only the currently attached host devices. What would be the most efficient way to configure MAC-level security on all these ports?
A. Visually verify the MAC addresses and then telnet to the switches to enter the switchport-port security mac-address command.
B. Have end users e-mail their MAC addresses. Telnet to the switch to enter the switchport-port security mac-address command.
C. Use the switchport port-security MAC address sticky command on all the switch ports that have end devices connected to them.
D. Use show mac-address-table to determine the addresses that are associated with each port and then enter the commands on each switch for MAC address port-security.
Answer: C
Explanation
We can use the “interface range” command (for example “interface range FastEthernet 0/1 – 48”) to configure many ports as the same time and use the “port-security MAC address sticky” command (without a specific MAC address) to dynamically learn the attached MAC Address and place it into the switch’s running-configuration -> C is correct.


