Port Security Questions
Question 1
Explanation
Follow these guidelines when configuring port security:
+ Port security can only be configured on static access ports, trunk ports, or 802.1Q tunnel ports. -> A is not correct.
+ A secure port cannot be a dynamic access port.
+ A secure port cannot be a destination port for Switched Port Analyzer (SPAN).
+ A secure port cannot belong to a Fast EtherChannel or Gigabit EtherChannel port group. -> D is not correct
+ You cannot configure static secure or sticky secure MAC addresses on a voice VLAN. -> B is not correct.
+ When you enable port security on an interface that is also configured with a voice VLAN, you must set the maximum allowed secure addresses on the port to at least two.
+ If any type of port security is enabled on the access VLAN, dynamic port security is automatically enabled on the voice VLAN.
+ When a voice VLAN is configured on a secure port that is also configured as a sticky secure port, all addresses seen on the voice VLAN are learned as dynamic secure addresses, and all addresses seen on the access VLAN (to which the port belongs) are learned as sticky secure addresses.
+ The switch does not support port security aging of sticky secure MAC addresses.
+ The protect and restrict options cannot be simultaneously enabled on an interface.
Note: Dynamic access port or Dynamic port VLAN membership must be connected to an end station. This type of port can be configured with the “switchport access vlan dynamic” command in the interface configuration mode. Please read more about Dynamic access port here: http://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst3550/software/release/12-1_19_ea1/configuration/guide/3550scg/swvlan.html#wp1103064
Question 2
Explanation
Host A (172.19.1.1) and the management IP address of the Switch (172.19.1.250) are in the same subnet so telnet from host A to the switch can be successful even if a default gateway is not set on host A.
But host B (172.19.32.2) and the management IP address of the Switch (172.19.1.250) are not in the same subnet so host B needs a default gateway to telnet to the switch. The default gateway on host B should be 172.19.32.254.
Question 3
Explanation
Shutdown is the default switch port port-security violation mode. When in this mode, the switch will automatically force the switchport into an error disabled (err-disable) state when a violation occurs. While in this state, the switchport forwards no traffic. The switchport can be brought out of this error disabled state by issuing the errdisable recovery cause CLI command or by disabling and re-enabling the switchport.
Question 4
Explanation
By default, port security limits the MAC address that can connect to a switch port to one. If the maximum number of MAC addresses is reached, when another MAC address attempting to access the port a security violation occurs.
Question 5
Explanation
Port security is only used on access port (which connects to hosts) so we need to set that port to “access” mode, then we need to specify the maximum number of hosts which are allowed to connect to this port -> C is correct.
Note: If we want to allow a fixed MAC address to connect, use the “switchport port-security mac-address ” command.
Question 6
Explanation
The full syntax of the second command is:
switchport port-security mac-address sticky [MAC]
If we don’t specify the MAC address (like in this question) then the switch will dynamically learn the attached MAC Address and place it into your running-configuration -> B is correct.
Question 7
Explanation
The first command 2950Switch(config-if)#switchport port-security is to enable the port-security in a switch port.
In the second command 2950Switch(config-if)#switchport port-security mac-address sticky, we need to know the full syntax of this command is switchport port-security mac-address sticky [MAC]. The STICKY keyword is used to make the MAC address appear in the running configuration and you can save it for later use. If you do not specify any MAC addresses after the STICKY keyword, the switch will dynamically learn the attached MAC Address and place it into your running-configuration. In this case, the switch will dynamically learn the MAC address 0000.00aa.aaaa of host A and add this MAC address to the running configuration.
In the last command 2950Switch(config-if)#switchport port-security maximum 1 you limited the number of secure MAC addresses to one and dynamically assigned it (because no MAC address is mentioned, the switch will get the MAC address of the attached MAC address to interface fa0/1), the workstation attached to that port is assured the full bandwidth of the port.Therefore only host A will be allowed to transmit frames on fa0/1 -> B is correct.
After you have set the maximum number of secure MAC addresses for interface fa0/1, the secure addresses are included in the “Secure MAC Address” table (this table is similar to the Mac Address Table but you can only view it with the show port-security address command). So in this question, although you don’t see the MAC address of host A listed in the MAC Address Table but frames with a destination of 0000.00aa.aaaa will be forwarded out of fa0/1 interface -> D is correct.
Question 8
Explanation
We can verify whether port security has been configured by using the “show running-config” or “show port-security interface ” for more detail. An example of the output of “show port-security interface ” command is shown below:
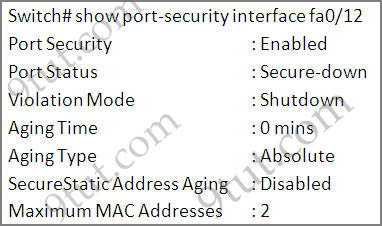
Question 9
Explanation
As we see in the output, the “Port Security” is in “Disabled” state (line 2 in the output). To enable Port security feature, we must enable it on that interface first with the command:
SwitchA(config-if)#switchport port-security
-> B is correct.
Also from the output, we learn that the switch is allowing 2 devices to connect to it (switchport port-security maximum 2) but the question requires allowing only PC_A to access the network so we need to reduce the maximum number to 1 -> D is correct.
Question 10
Which condition does the err-disabled status indicate on an Ethernet interface?
A. There is a duplex mismatch.
B. The device at the other end of the connection is powered off.
C. The serial interface is disabled.
D. The interface is configured with the shutdown command.
E. Port security has disabled the interface.
F. The interface is fully functioning.
Answer: E
Explanation
There are various reasons for the interface to go into errdisable. The reason can be:
+ Duplex mismatch
+ Port channel misconfiguration
+ BPDU guard violation
+ UniDirectional Link Detection (UDLD) condition
+ Late-collision detection
+ Link-flap detection
+ Security violation
+ Port Aggregation Protocol (PAgP) flap
+ Layer 2 Tunneling Protocol (L2TP) guard
+ DHCP snooping rate-limit
+ Incorrect GBIC / Small Form-Factor Pluggable (SFP) module or cable
+ Address Resolution Protocol (ARP) inspection
+ Inline power
Therefore in fact there are two correct answers in this question, which are “There is a duplex mismatch” and “Port security has disabled the interface” but maybe you should choose the port security answer as it is the most popular reason.


