SNMP Questions
Note: If you are not sure about SNMP, please read our SNMP tutorial.
Question 1
Explanation
The user-based access control implemented by SNMPv3 is based on contexts and user names, rather than on IP addresses and community strings. It is a partial implementation of the view-based access control model (VACM).
Question 2
Explanation
The first step we need to do when configuring an SNMPv3 user is to configure the server group to enable authentication for members of a specified named access list via the “snmp-server group” command. For example:
| Router(config)# snmp-server group MyGroup v3 auth access snmp_acl |
In this example, the SNMP server group MyGroup is configured to enable user authentication for members of the named access list snmp_acl.
Question 3
Explanation
Default values do not exist for authentication or privacy algorithms when you configure the SNMP commands. Also, no default passwords exist. The minimum length for a password is one character, although we recommend that you use at least eight characters for security. If you forget a password, you cannot recover it and must reconfigure the user. You can specify either a plain text password or a localized Message Digest 5 (MD5) digest.
Question 4
Explanation
Three security models are available: SNMPv1, SNMPv2c, and SNMPv3. The security model combined with the security level determine the security mechanism applied when the SNMP message is processed.
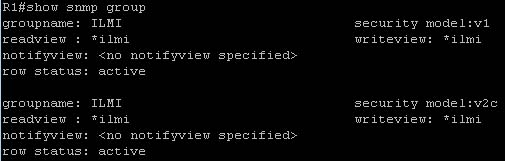
The command “show snmp group” displays the names of groups on the router and the security model, the status of the different views, and the storage type of each group. Below is an example of this command.
Question 5
Explanation
The “show snmp pending” command displays the current set of pending SNMP requests. It also displays the SNMP version used.
Router# show snmp pending req id: 47, dest: 171.69.58.33.161, V2C community: public, Expires in 5 secs req id: 49, dest: 171.69.58.33.161, V2C community: public, Expires in 6 secs req id: 51, dest: 171.69.58.33.161, V2C community: public, Expires in 6 secs req id: 53, dest: 171.69.58.33.161, V2C community: public, Expires in 8 secs
Note:
The “show snmp engineID” displays the identification of the local SNMP engine and all remote engines that have been configured on the router. The following example specifies 00000009020000000C025808 as the local engineID and 123456789ABCDEF000000000 as the remote engine ID, 171.69.37.61 as the IP address of the remote engine (copy of SNMP) and 162 as the port from which the remote device is connected to the local device:
Router# show snmp engineID Local SNMP engineID: 00000009020000000C025808 Remote Engine ID IP-addr Port 123456789ABCDEF000000000 171.69.37.61 162
Question 6
Explanation
SNMPv1/v2 can neither authenticate the source of a management message nor provide encryption. Without authentication, it is possible for nonauthorized users to exercise SNMP network management functions. It is also possible for nonauthorized users to eavesdrop on management information as it passes from managed systems to the management system. Because of these deficiencies, many SNMPv1/v2 implementations are limited to simply a read-only capability, reducing their utility to that of a network monitor; no network control applications can be supported. To correct the security deficiencies of SNMPv1/v2, SNMPv3 was issued as a set of Proposed Standards in January 1998. -> A is correct.
(Reference: http://www.cisco.com/web/about/ac123/ac147/archived_issues/ipj_1-3/snmpv3.html)
The two additional messages are added in SNMP2 (compared to SNMPv1)
GetBulkRequest The GetBulkRequest message enables an SNMP manager to access large chunks of data. GetBulkRequest allows an agent to respond with as much information as will fit in the response PDU. Agents that cannot provide values for all variables in a list will send partial information. -> E is correct.
InformRequest The InformRequest message allows NMS stations to share trap information. (Traps are issued by SNMP agents when a device change occurs.) InformRequest messages are generally used between NMS stations, not between NMS stations and agents. -> C is correct.
Note: These two messages are carried over SNMPv3.
Question 7
Explanation
You can assign views to community strings to limit which MIB objects an SNMP manager can access. The syntax to create a view record is shown below:
Router(config)# snmp-server view view-name oid-tree {included | excluded}
Reference: https://www.cisco.com/c/en/us/td/docs/ios/12_2/configfun/configuration/guide/ffun_c/fcf014.html



It would be great if there were a better explanation for all the questions, i have to memorize some of them